Zumpfun
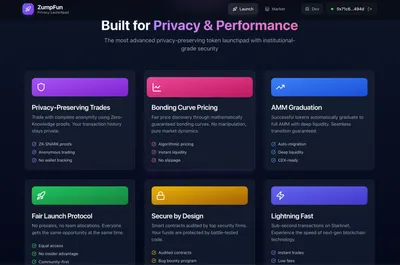
Privacy-first token creation platform on ztarknet
Awards
The problem it solves
ZumpFun: Privacy-Preserving Meme Coin Launchpad
ZumpFun solves critical privacy and fairness issues in meme coin launches:
Privacy Problems Solved:
- Visible Trading Activity: On traditional platforms like Pump.fun, everyone can see who’s buying, how much, and when—leading to front-running and whale manipulation. ZumpFun uses Noir ZK proofs with Pedersen commitments to hide contribution amounts completely.
- Identity Exposure: Creators and early contributors are publicly linked to tokens, exposing them to doxxing and targeted attacks. ZumpFun enables anonymous contributions while proving eligibility via zero-knowledge Merkle proofs.
- Whale Tracking: Large holders are easily identified and manipulated. ZumpFun’s nullifier system prevents tracking of individual trading patterns.
Use Cases:
- Launch tokens anonymously without revealing creator identity
- Contribute to launches privately - amount hidden via ZK commitments
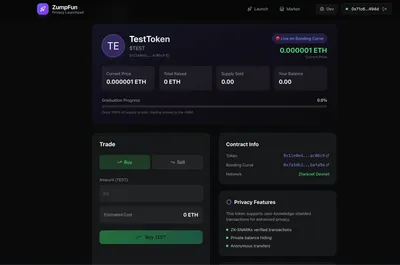
- Fair price discovery via sigmoid bonding curve (same mechanics as Pump.fun)
- Automatic DEX graduation at 800M tokens → Ekubo AMM
- Selective disclosure - reveal only what you choose (e.g., prove you contributed $1000+ without showing exact amount)
Tech Stack: Cairo smart contracts + Noir circuits + Garaga on-chain verification on Ztarknet
Challenges we ran into
- Noir’s New map API Breaking 45+ Tests
The biggest hurdle was Noir’s transition from the old HashMap API to the new functional BTreeMap with map() method. Every circuit test failed because map no longer took a closure the same way.
Solution: Rewrote all 45+ instances to use the new pattern: // Old (broken) let result = items.map(|x| transform(x));
// New (working) let result = items.iter().map(transform).collect();
- Garaga Integration Complexity
Garaga’s on-chain verifier requires Ultra KZG Honk proofs with specific formatting. The Barretenberg prover output didn’t match Garaga’s expected input format initially.
Solution: Used garaga gen —system ultra_kzg_honk to generate Cairo verifier code directly from our Noir circuits, ensuring compatibility.
- Ztarknet Devnet Connectivity
The Ztarknet devnet at ztarknet-madara.d.karnot.xyz had intermittent connection issues and required specific Madara-compatible transaction formats.
Solution: Created deployment scripts with retry logic and proper fee estimation for the Madara stack.
- Cairo 2.14 Migration
Had to migrate from older Cairo syntax to Cairo 2.14’s stricter type system, particularly around ByteArray and storage handling.
Solution: Updated all contracts to use proper felt252 conversions and the new #[storage] macro syntax.